Network security concepts in school safety plans
As summer nears its end, there's a lot of discussion about how and when to reopen schools and universities. As a security professional, I can't help but see the parallels between protecting students and faculty from a pandemic and protecting networks from malware. This post will examine those similarities from a network security prospective (for those who say that a security professional has no place discussing education during a pandemic, I would agree as my friends in education tell me that a zoo-keeper would be much better qualified).
In olden days, much of network security was focused on the perimeter. Like the walls of a city, one could hold off attacks and control traffic in and out, searching for contraband malware as packets came and went. Today the perimeter is still an important part of the network. Traffic is regulated, incoming and outgoing files and emails are scanned and communication is monitored for anomalies. In a school this is where a lot of the focus is. Students and staff are "scanned" before entering, attendance is taken regularly and potential threats are sent home.
Nowadays, bring your own device (BYOD), persistent threats and an increased dependence on external services have shown that perimeter security while still necessary, is no longer sufficient to protect the network. BYOD policies mean that devices on the network, can not be monitored and controlled at all times, introducing a risk of a device being infected outside of the network and bringing the infection in. This is similar to the threat faced in public schools around the country as children return home each day. While a boarding school in an isolated location may a much different threat model. Persistent adversaries, such as organized crime rings and nation states will patiently wait for an opening, taking advantage as soon as they find one. While the COVID-19 virus may one day turn to something that happens in sporadic outbreaks, for now it is ubiquitous, much like a persistent threat. As the enterprise relies more and more on internet based software as a service (Saas) solutions, the points of exposure increase. School are not just teachers and students, but rely on vendors for supplies and food, sometimes outsourcing services such as cleaning, cooking and IT support to third parties who have other clients.
The "defense in depth" model assumes that a breach of the perimeter is an eventuality and aims to contain that breach as best as possible through network segmentation and intrusion detection. If the outer walls of a city fell, there may be inner walls or the castle itself where the "important" resources were kept (food, weapons, treasure, royal personage…). On today's networks, this is accomplished via network segmentation. The goal of network segmentation is making it harder to transverse through the network in the event that an endpoint is compromised. For example, a company's website is likely available to the entire internet, increasing its exposure and likelihood of compromise. Proper network segmentation would ensure that a companies website server would have no way of directly communicating with its HR or payroll servers. Schools and universities are following the same principals, allowing those who can to work from home, limiting the interaction of different departments and possibly segmenting students into "self contained" cohorts.
Intrusion detection aims to detect when a device is compromised and alert on it. This is typically accomplished either through network based or host based agents. The network based model analyzes network traffic for malicious activity, potentially a teacher noticing a student coughing or administering temperature checks on arrival and may log results or even network traffic (which students went to the bathroom when…). In the host based model, the onerous is on the individual device, this is usually agents scanning the device for malware or unusual activity. This may be a student reporting that they don't feel well, going for a private test or being aware of places they've gone and proactively checking for exposures. Malware, like a an infection may be easy or hard to spot. Ransomware for instance, often time encrypts all your files and displays a note, whereas a data exfiltration program may purposely make itself hard to detect. For this reason malware protection uses both heuristic and definition based detection. Heuristic detection relies on spotting changes in behavior such as a service reaching out to a shady darknet site, or a student coughing. Definition based detection relies on spotting known patterns in a file or process, such as the hash of a file or a positive test result. Modern antivirus solutions usually rely on both methods for detection.
Finally, its common knowledge that having an incident is not a matter of if, but when. With the pervasive nature of the pandemic schools can expect some sort of an incident to occur. This may be a full blown outbreak, a confirmed exposure, a symptomatic individual or an interruption of a critical supply chain. When an incident does occur, the incident response playbook is activated and the incident response lifecycle kicks off
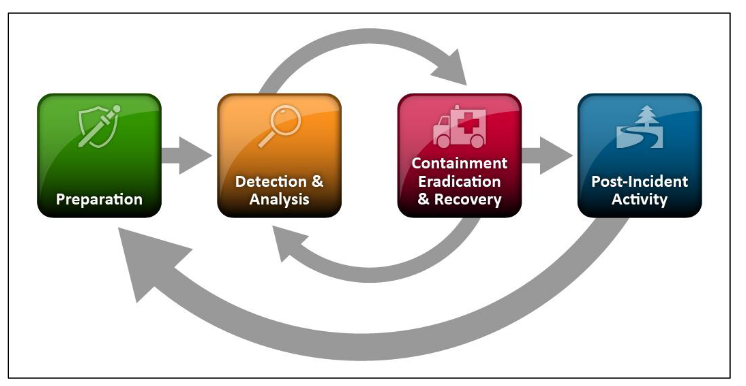
In the preparation phase, the teams are created, tabletop exercises (simulations) may be run, playbooks are written and the tooling is configured and monitored. The incident response team is composed of representatives from around the organization. Not just IT, but also legal, finance, HR and whoever else may be necessary. Its important for an organization to ensure team is ready before an incident occurs and that everyone is aware of what their roles and responsibilities are. In a school or university this may include members of the staff, student representatives, parents, vendors and union representatives. In the event of an incident, its also important to remember that your systems may not be working, email may be down or compromised, computers may be bricked. During an incident, a company will often times rely on 3rd party email accounts, separate laptops that are "off the network", personal phones… When responding to an outbreak, schools will have to plan for staff who may be sick and unable to preform their role in incident response. For this scenario, having backup team members who don't regularly interact with each other could be a viable option. Lastly, incident response is a cycle, lessons learned during the post incident review should be used to create better preparation and detection capabilities for the future.
Operating schools in a pandemic is a challenge to say the least. The way that schools plan for, detect and respond to incidents share several similarities with the way network security professionals do the same. One day this pandemic will be over, but even then the principals of risk management and incident response will continue to help keep students and faculty safe from whatever incidents or disasters come their way.